The Most Targeted. The Most Expensive
Why Healthcare MUST Have SIEM Monitoring
Simply put, healthcare is one of the easiest industries to hack, and the most catastrophic to recover from.
For 14 consecutive years, healthcare has topped the list for the highest average breach cost $9.77 million per incident in 2024 (IBM Cost of Data Breach 2024). In the same year, 67% of healthcare organisations suffered ransomware attacks , a four year high while the overall ransomware rate across all other industries actually fell (Sophos 2024).
Ransomware attacks on healthcare have surged 300% since 2015, and between 2016 and 2021, researchers estimate they contributed to the deaths of between 42 and 67 patients (IBM; HIPAA Journal).
Clearly, this is a serious patient safety issue that we all should emphasize on.
Why Healthcare Is a Perfect Target?
Many users, many accounts — nurses, doctors, interns, and vendors all need access, creating a hard-to-manage attack surface
Limited cybersecurity budget — investment goes to clinical systems, not security monitoring
Small IT teams, many vendors — only 14% of healthcare organisations say their IT security teams are fully staffed (IBM 2024)
Multiple locations — HQ, branch clinics, labs, pharmacies, and specialist centres with inconsistent security standards and no centralised visibility
24/7 operations — IoT equipment and outdated Windows servers that cannot be patched without disrupting clinical operations
Patient data extraordinarily valuable — a medical record sells for $50–$250 on the dark web, compared to $5–$10 for a credit card, because it contains the full identity: IC/passport, address, insurance data, diagnosis, prescriptions, and billing history (dark web market research)
What Attackers Want?
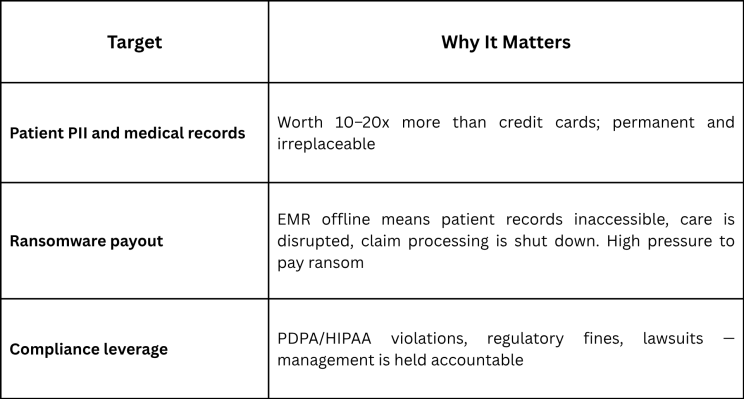
As a result, the average healthcare ransom payment in 2024: $1.5 million with 57% of victims paying more than the original demand. Furthermore, the mean recovery cost, excluding the ransom: $2.57 million (Sophos 2024).

How Attackers Enter a Hospital
Consider these common entry points, all exploited because of weak hygiene, not sophistication:
Phishing a staff email — busy, shift-based medical staff are among the most phishing-prone workforces in any industry
Compromised nurse or doctor credentials — stolen passwords reused across systems
Unpatched lab systems — known vulnerabilities, never fixed due to operational constraints
Insecure IoT and medical devices — connected equipment with no authentication and outdated firmware
“I Already Have a Firewall and Antivirus. Why Do I Need SIEM?“
Yes, firewall and antivirus protect the perimeter. Once an attacker is inside, through phishing, a stolen credential, or an unpatched device, those tools go completely blind.
For instance, they cannot tell you:
That a nurse account logged in at 3AM from an unfamiliar device
That someone exported 50,000 patient records to an external drive
That an attacker has been moving between lab servers and EMR systems for three weeks
That an unknown device appeared on your network and is scanning internal systems
Abatis365 sees what perimeter tools cannot monitoring behaviour inside the network, correlating events across all systems, and alerting your team before a containable incident becomes a catastrophic breach.
What Abatis365 Detects — Before the Damage Is Done
1. Identity and Access:
Interns or nurses accessing VIP patient records outside their clinical role
Privilege misuse and unauthorised account changes
After-hours access to EMR/EHR from unusual devices or locations
2. Data and System:
Mass patient record exports outside normal clinical workflows
Abnormal encryption behaviour and shadow copy deletion
Suspicious PowerShell usage and unknown processes spreading
3. Network:
Lateral movement between servers and clinical systems
Unknown IP communication and unexpected external connections
Unusual network scanning and abnormal device traffic
The Real Cost of Not Having SIEM
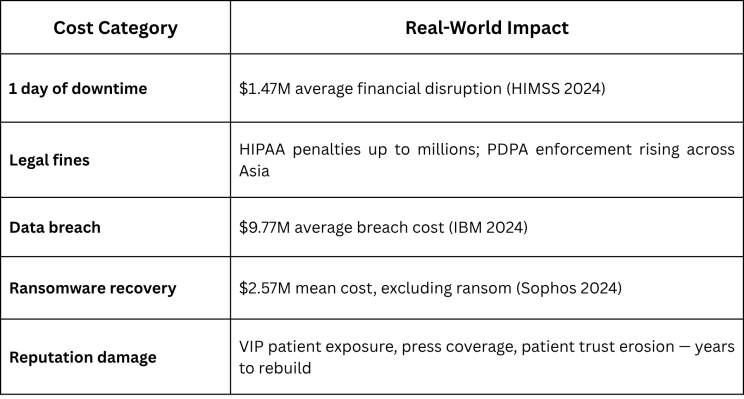
The cost of one day of downtime alone exceeds most annual SIEM investment budgets.
The Bottom Line
Healthcare cannot afford downtime. Therefore, SOC monitoring is not an IT cost. It is clinical risk management.
If your hospital or clinic network doesn’t have 24/7 SIEM monitoring today, your patients’ data and your organisation’s reputation, are already at risk.
Want to know where your current blind spots are?
Abatis365 provides centralised 24/7 monitoring across EMR systems, branch clinics, labs, and third-party access, all from a single dashboard, without disrupting care delivery. Let’s talk.

