Energy and Mining Sector Is Under Attack
How to guard your safety and uptime?
The energy and mining sector is one of the most targeted industries in cybersecurity. In fact, Ransomware groups deliberately prioritise critical infrastructure, not because it is easy to breach, but because the impact of downtime is catastrophic and the pressure to pay is immediate.
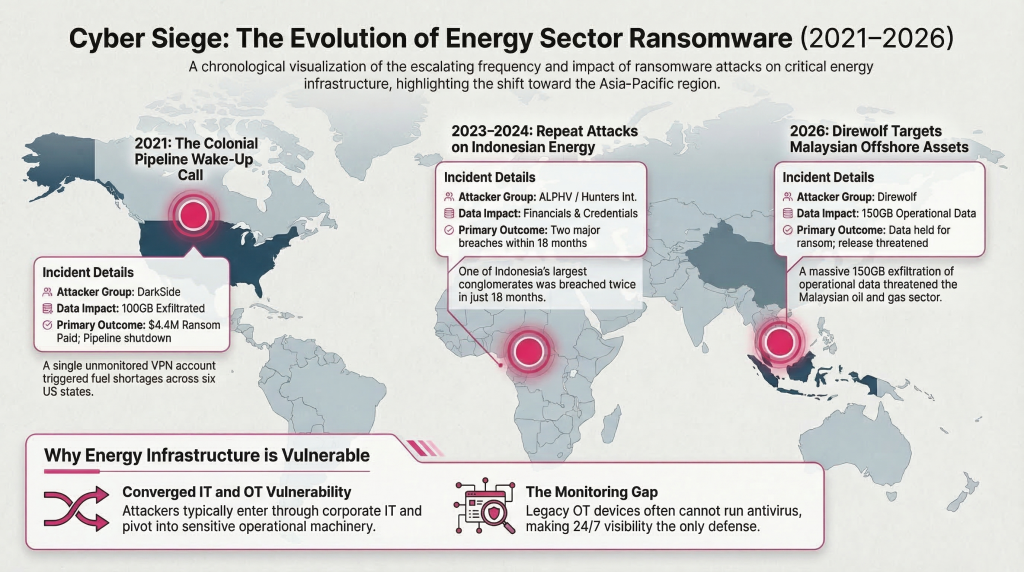
The Global Wake-Up Call: Colonial Pipeline (2021)
In May 2021, Colonial Pipeline supplying 45% of fuel to the US East Coast shut down entirely. Surprisingly, the entry point was not a sophisticated exploit. It was one dormant VPN account with no MFA, whose password had been exposed in a prior breach and never rotated (US DoJ; Mandiant).
What followed:
DarkSide ransomware moved laterally through IT systems, exfiltrating ~100GB of data
Furthermore, with no OT visibility, Colonial couldn’t confirm how far the threat had spread
As a precaution, Colonial shut down the pipeline — triggering fuel shortages across six US states
$4.4 million ransom paid (US DoJ)
One unmonitored account. One blind spot. Billions in consequences
It Is Happening Across Asia Pacific Too
Indonesia — PT Indika Energy (2023–2024) One of Indonesia’s largest energy conglomerates ($3B revenue) was hit twice: ALPHV ransomware in February 2023, then Hunters International in July 2024. Both attacks involved data exfiltration, financial statements, employee records, and partner credentials. Two breaches in 18 months. Notably, conventional IT security stopped neither attack.
Malaysia — Perdana Petroleum Berhad (2026) On January 13, 2026, the Direwolf ransomware group claimed responsibility for attacking this Malaysian offshore oil and gas services company. 150GB of operational data, which the group then threatened to release publicly.
Importantly, these are not isolated incidents. Across Asia-Pacific, energy organisations in Vietnam, Indonesia, Pakistan, and Australia have all been targeted in recent years:
Why Energy and Mining Is So Hard to Protect
A. Highly Distributed Assets
Remote substations, offshore platforms, and rural mine sites cannot be physically inspected
Security teams have no hands on visibility, digital monitoring is the only option
B. Converged IT and OT Environments
To understand the risk, consider that modern energy and mining operations run on two interconnected layers:
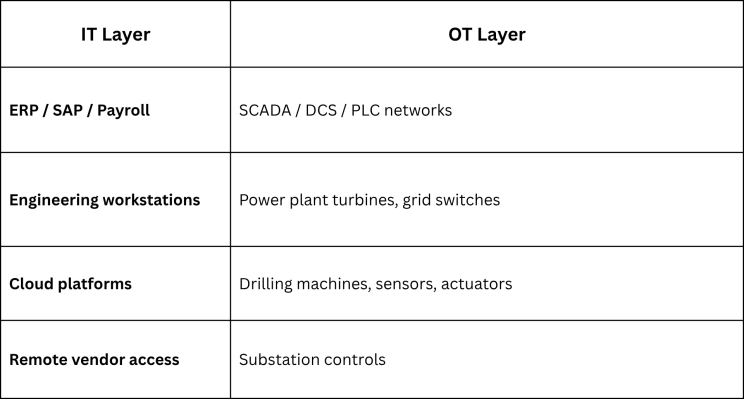
Attackers enter from IT and pivot into OT. The attack path is well established:
Office PC → Engineer laptop → SCADA server → PLC → Machine overload
Phish an employee email
Install malware on an engineer’s laptop
Move laterally to SCADA server
Change PLC settings
Machine overloads → production stops, millions lost
As a result, a cyber attack becomes physical damage.
C. OT Is Harder to Secure Than IT
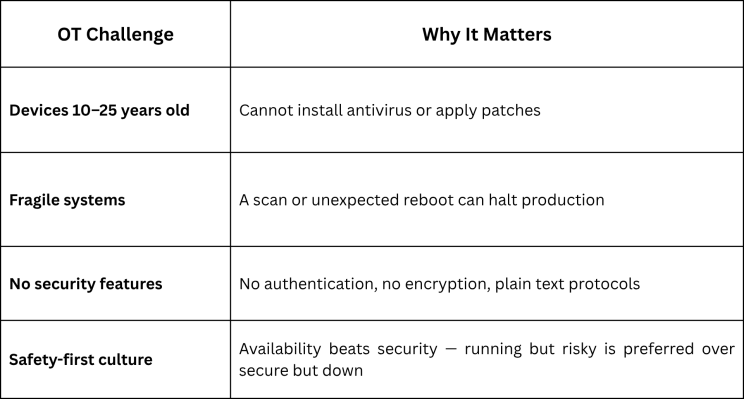
You cannot protect OT like IT. You can only monitor it.
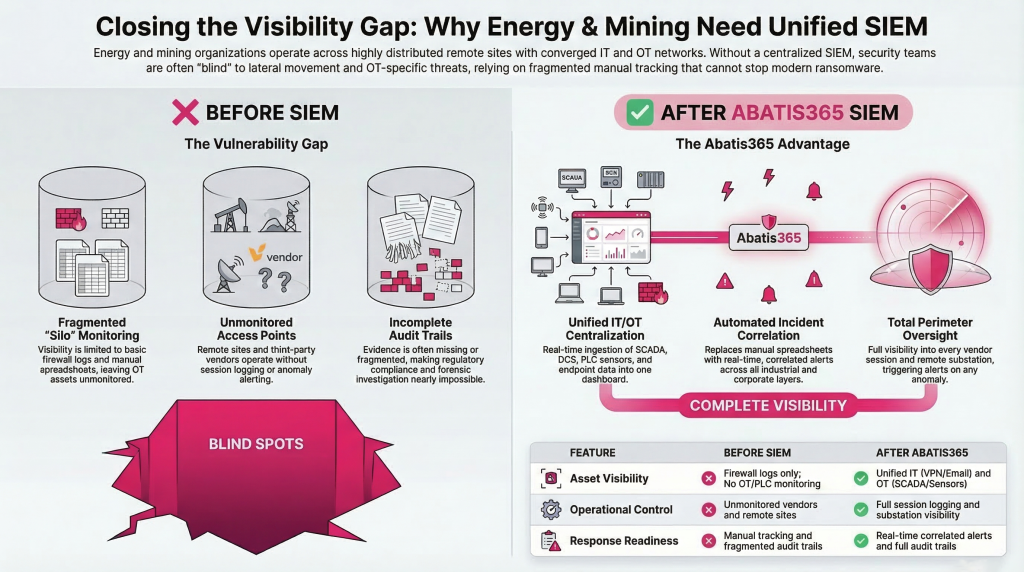
What Abatis365 Monitors in Energy and Mining
A properly deployed SIEM provides end to end attack path visibility that prevents a contained incident from becoming catastrophic:
Dormant and anomalous credential usage
Data exfiltration patterns
IT to OT lateral movement
Unauthorized firmware changes, PLC and Scada monitoring
Suspicious remote sessions running longer than expected, from unexpected locations

Energy and mining organisations run on daily yield, production targets, and operational uptime. Cybersecurity feels distant, until a ransomware group shuts down a pipeline, encrypts a mining ERP, or exfiltrates 150GB of offshore operational data.
The organisations that were hit were not negligent. Rather, they were focused on operations, the same way yours is. The difference between them and a prepared organisation is visibility.
24/7 SIEM monitoring with Abatis365 doesn’t slow your operations down. Instead, it makes sure nothing else does either.
If your energy or mining operation doesn’t have SIEM monitoring running today, Abatis365 works with energy and mining operators across Asia Pacific starting with an honest assessment before any deployment. Let’s Talk.

