Manufacturing Is the #1 Ransomware Target Globally — Is Your Factory Ready?
A CISO Perspective on Protecting IP, Production, and Operational Continuity with SIEM
Manufacturing has been the most targeted industry for ransomware for three consecutive years. In 2024, 47% of all manufacturing breaches involved ransomware and attacks surged 61% year on year in 2025 (Verizon DBIR 2025; KELA). One hour of stopped production can cost more than an entire year of SIEM and SOC investment combined. Yet most manufacturing environments remain critically under monitored.
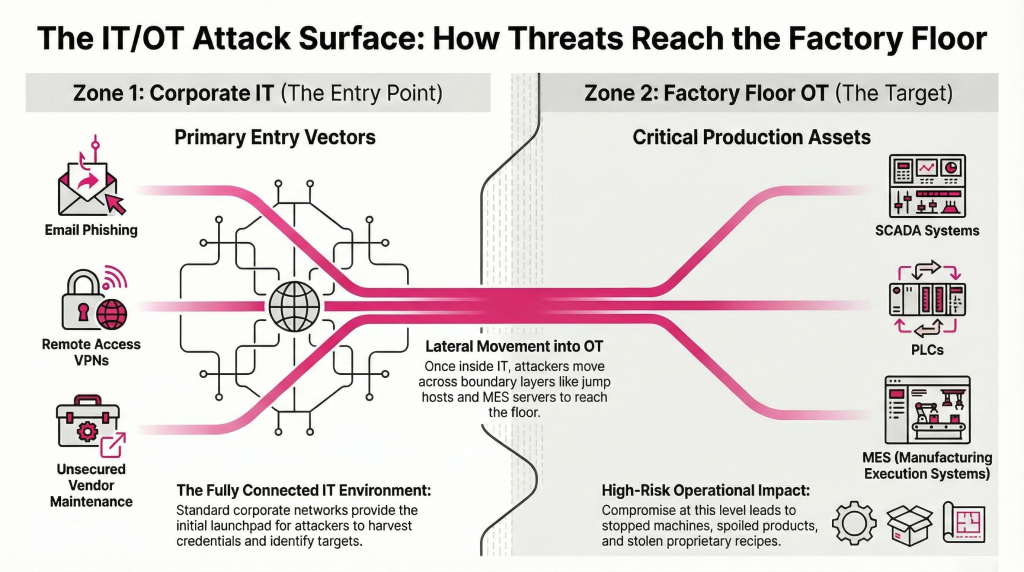
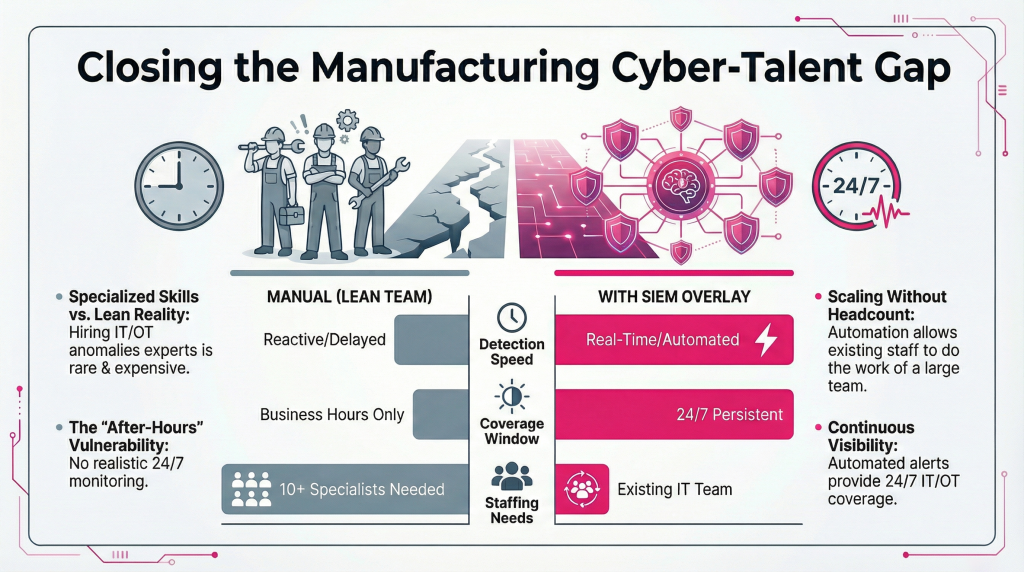
The reason isn’t ignorance. It’s complexity, talent scarcity, and a dangerous assumption that the factory floor is somehow separate from the threat landscape.
It isn’t.
Why Manufacturing Is an Irresistible Target
Manufacturing sits at the intersection of everything attackers want most:
Valuable IP and secrets: proprietary recipes, patented designs, R&D data, fabrication processes, and formulations built over decades
Production that cannot stop: every hour of downtime directly destroys revenue and triggers contractual penalties
Low cyber maturity: investment goes into ERP, PLCs, and production systems — never about security
Fragmented, siloed visibility: multiple brands of firewalls, PLC/OT devices, ERP, cloud, WMS, and CCTV all operate separately with no single view across the environment
High-value data beyond IP: customer NDA data, supplier contracts, and pricing intelligence that competitors want
Weak cyber hygiene: unpatched servers, shared credentials, no EDR on workstations, OT devices that cannot be updated
Firewall and antivirus alone will not detect or stop these attacks. They were not designed for lateral movement, slow exfiltration, and OT-layer threats.
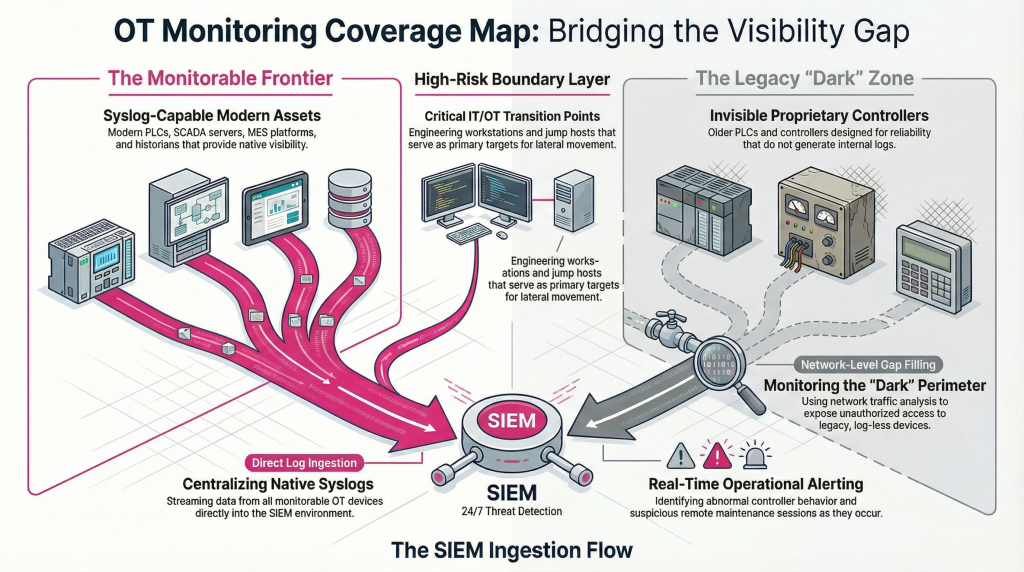
OT Monitoring: What's Possible, What's Not
An honest truth most vendors skip: you cannot monitor every OT device. Many cannot generate logs without risking production uptime.
But here’s what you can, and must monitor today:
Any OT device that generates syslogs — SCADA servers, modern PLCs, MES, historians, IIoT sensors — should feed your SIEM
Remote vendor sessions and VPN access are your highest-risk entry points and are fully monitorable
Every syslog capable device you aren’t monitoring today is a blind spot an attacker looking for.
Why 24/7 Monitoring Is Non-Negotiable
Manufacturing doesn’t stop at 5PM. Neither do attackers. Experienced threat actors deliberately target nights, weekends, and public holidays when no one is watching.
The average attacker dwell time in manufacturing before detection is 277 days(NIST 2024). Without 24/7 SIEM monitoring, exfiltration runs silently for months.Before Abatis365 vs. After Abatis365
Early Warnings Abatis365 Delivers Before Damage Occurs
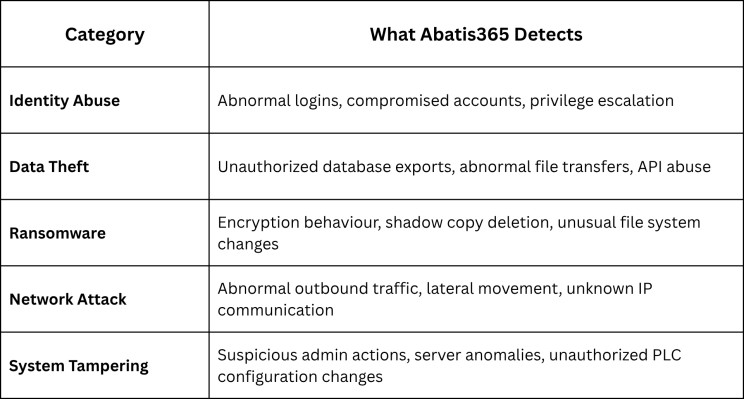
These signals, correlated across IT and OT layers by Abatis365, tell the full attack story, before the production line stops.
Before Abatis365 vs After Abatis365
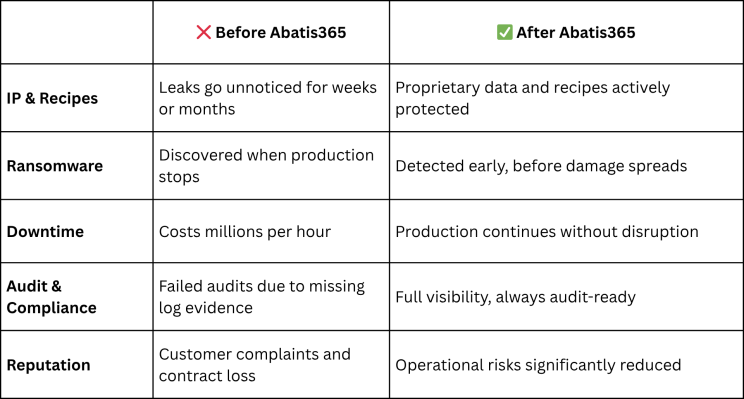
You only know what’s wrong when the damage is done, or you have Abatis365 watching 24/7.
Manufacturing is the #1 ransomware target globally. Your production data, IP, and recipes are being actively pursued. Firewall and antivirus won’t stop it. But visibility will give you more understanding of your environment.
Thinking about where to start with IT/OT monitoring? We work with manufacturers at every stage from initial visibility assessments to full SIEM deployment. No pitch, no pressure. Let’s talk.

